Your data is safe in our hands. Really.
Security best practices are built into every layer of the LogicMonitor experience, from our technical architecture to our everyday business operations.
The LogicMonitor platform is certified to:
A representative will reach out shortly with next steps.
Get real-time insights and automation for comprehensive, seamless monitoring with agentless architecture.
Whether you work in MSP, Enterprise IT or somewhere in between, the solution is clear.
Get to know LogicMonitor and our team.
Read through our documentation, check out our latest release notes, or submit a ticket to our world-class customer service team.

Get real-time insights and automation for comprehensive, seamless monitoring with agentless architecture.





Whether you work in MSP, Enterprise IT or somewhere in between, the solution is clear.





Get to know LogicMonitor and our team.





Read through our documentation, check out our latest release notes, or submit a ticket to our world-class customer service team.
A representative will reach out shortly with next steps.
Security best practices are built into every layer of the LogicMonitor experience, from our technical architecture to our everyday business operations.
The LogicMonitor platform is certified to:

FINANCIAL SERVICES ORGANIZATION
GLOBAL IDENITY MANAGEMENT


HEALTHCARE EFFICIENCY SOFTWARE

Discover how hybrid observability empowers organizations to streamline monitoring, control costs, and enhance performance. With actionable insights and the power of LogicMonitor, embark on a successful cloud migration journey while fostering agility and innovation.
Learn More
LogicMonitor’s LM Envision redefines network monitoring for the modern era. From detecting anomalies to conquering alert fatigue, explore how this SaaS-based platform revolutionizes network modernization with AI-powered insights, ensuring price predictability and ease of use.
Learn More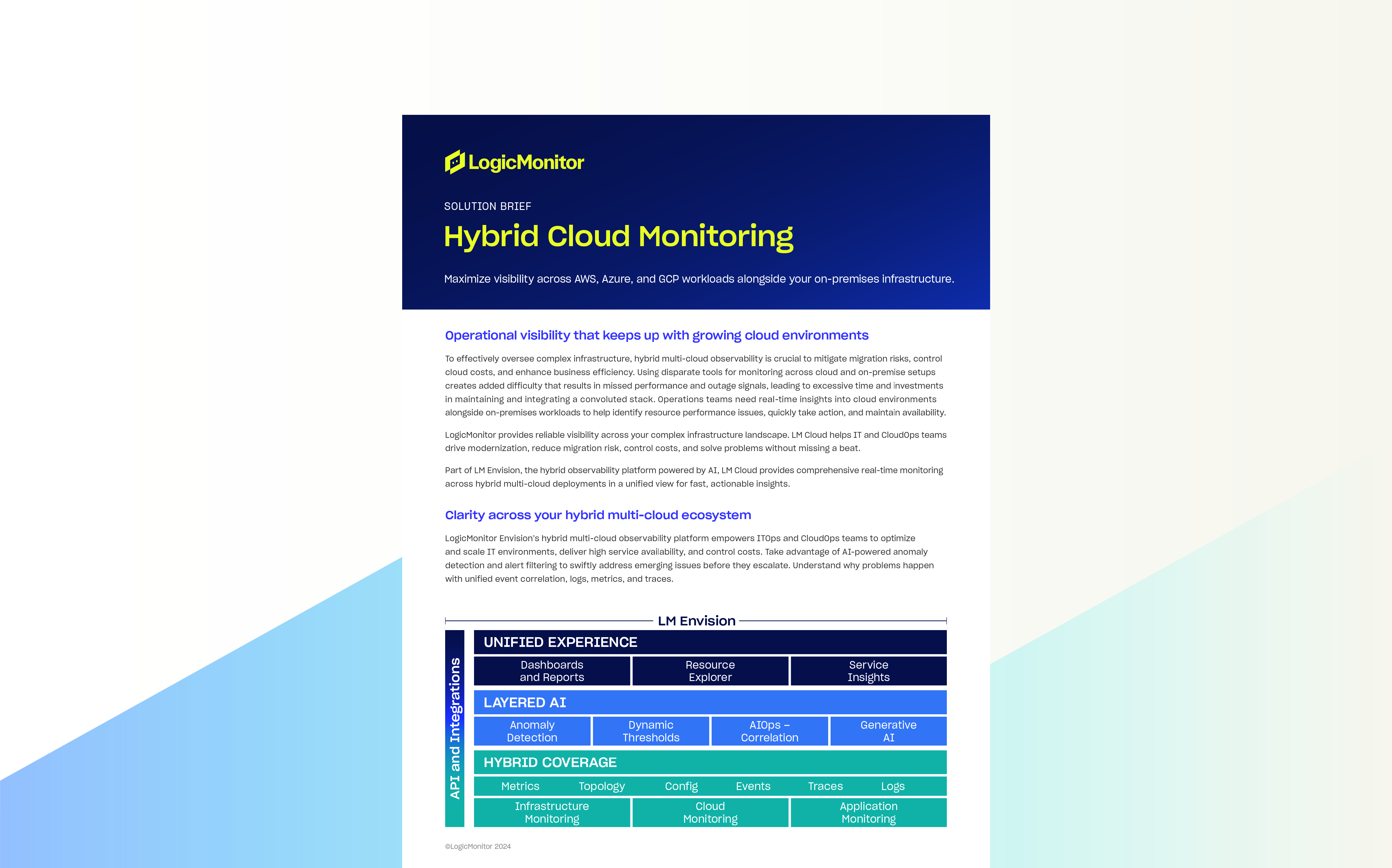
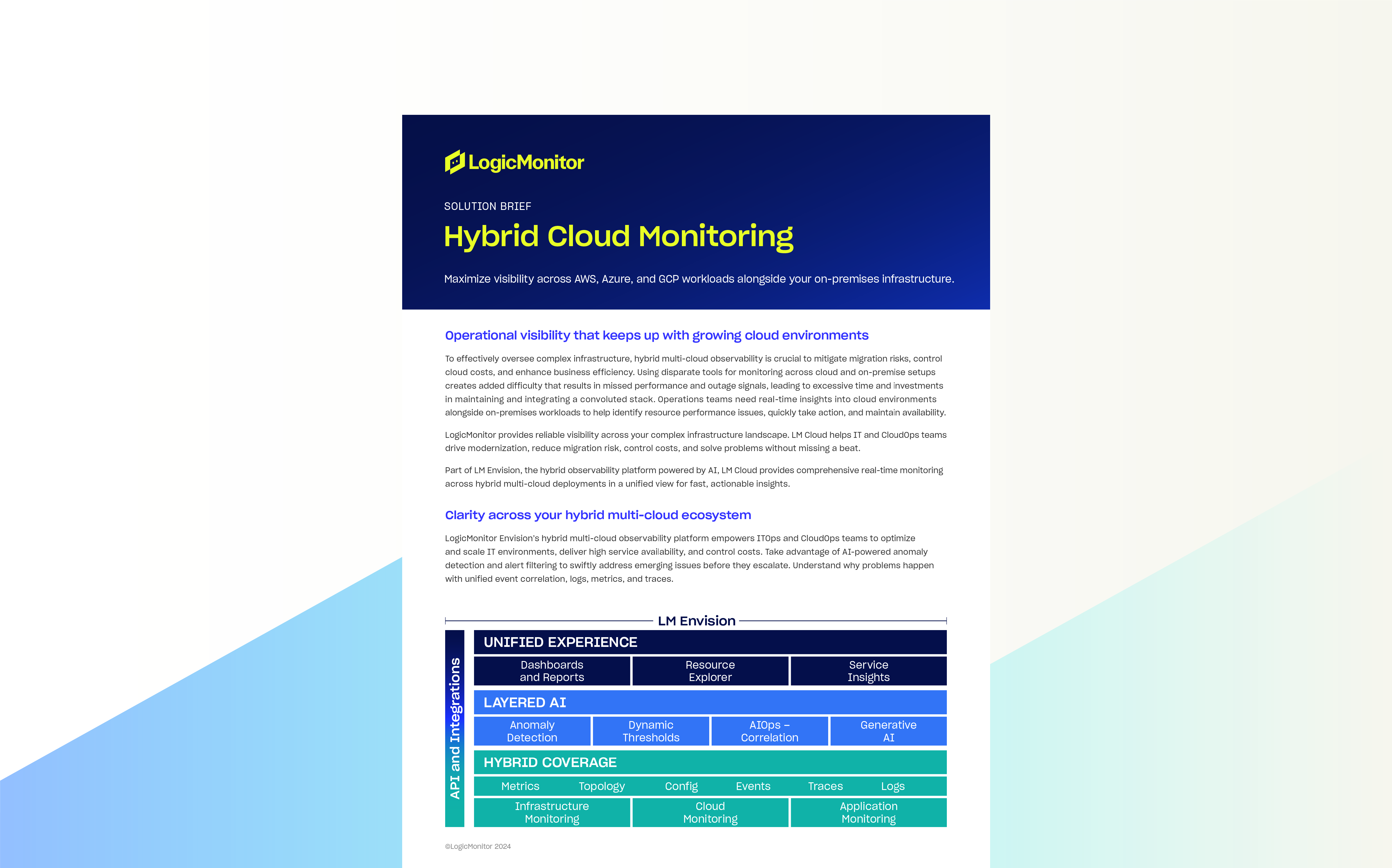
Discover how LogicMonitor’s Hybrid Cloud Monitoring solution provides comprehensive visibility across AWS, Azure, GCP, and on-premises infrastructure, empowering IT and CloudOps teams with real-time insights to optimize performance, mitigate risks, and control costs efficiently.
Learn More