BGP Hijacking
BGP has no built-in authentication, which means any AS can announce prefixes it doesn’t own. BGP hijacking exploits this to redirect or intercept internet traffic at scale. Here’s how it works and how to defend against it.
Denton Chikura
The quick download:
BGP hijacking exploits the protocol’s lack of built-in origin authentication to redirect internet traffic, and because BGP routes propagate globally in minutes, the impact can be enormous before anyone notices.
-
Any AS can announce any prefix, BGP has no built-in mechanism to verify that the announcing AS actually owns the prefix.
-
Hijacks range from accidental misconfigurations to deliberate attacks; both can cause massive traffic disruption or interception.
-
RPKI (Resource Public Key Infrastructure) provides cryptographic validation of route origin but adoption remains incomplete globally.
-
Implement RPKI validation and monitor your own prefixes from external vantage points continuously, waiting for a customer complaint to discover a hijack means the damage is already done.
Many activities essential to modern life depend on the internet, and the internet depends on the Border GatThe internet is the wild west of networking. Although there are rules, these rules can be broken at the drop of a hat, either accidentally or deliberately. Like the wild west, there is also the law. Sheriffs who oversee the behavior of citizens to ensurethey obey the rules. In much the same way, BGP monitoring is a vital tool used to ensure that owners of Autonomous Systems (AS) abide by the rules when it comes to which prefixes they announce and how they announce them.
One of the most common ways in which rules are broken on the internet is when a BGP router advertises a prefix that does not belong to its own AS. In other words, it illegitimately announces that specific prefix, thus redirecting traffic from its intended destination towards its own AS.
This is called BGP route hijacking, but is also known as prefix hijacking, route hijacking, and IP hijacking.
Remember, BGP is the only way throughwhich the world will know how to get to your specific IP address. If a BGP router illegimately announces, “Hey, if you want to get to this address, send all your traffic to me!” then you can imagine the havoc that will follow.
For example, in April of 2018, malicious hackers were able to announce some IP prefixes that belonged to Amazon Web Services. The result was that users attempting to log into a cryptocurrency site were redirected to a fake version of that site, putting in their credentials, and unknowingly depositing over $160,000 directly into the hackers’ wallets.
However, it’s not just malicious attacks that can cause damage. Unintentional instances of BGP hijacking can also have seriousconsequences. In 2008, an ISP in Pakistan attempted to censor YouTube by updating its BGP routes. An error in the configuration caused the whole internet to route YouTube traffic to the Pakistani ISP, resulting in an hours-long outage of YouTube worldwide, and an overwhelmed ISP.
In this chapter of our BGP monitoring guide, we’ll explore the topic of BGP hijacking in depth, including how BGP advertisements work, how bad actors perform hijacks, and how you can detect and prevent BGP route hijacking.
Executive summary
To mitigate BGP hijacks, it is important to understand the intricacies of how BGP works, how successful hijacking happens, the motives behind deliberate hijacking, and the causes of inadvertent hijacking. The following table summarizes the concepts that will be examined in detail in this article.
BGP Hijacking Overview
| Topic | Description |
|---|---|
| BGP advertising | Understand how BGP advertises and announces prefixes. |
| What is a BGP route hijack? | Examine in-depth the various scenarios that involve the hijacking of IP routes. |
| AS_PATH attribute | Learn how this BGP attribute can make hijacked routes more attractive than their actual originator ASes. |
| Prefix Mismatch | Find out why mismatching of the prefix can either inadvertently introduce hijacking or can make deliberate hijacking more successful. |
| Motives | Understand what moves malicious hackers to deliberately hijack prefixes? |
Understanding the fundamentals of BGP hijacking
Because BGP is designed with the assumption that all BGP “speakers” are telling the truth, BGP route hijacking is surprisingly simple. It’s truly mind boggling that if you administer a large ISP network, nothing is stopping you from issuing a few commands that can potentially bring the internet to its knees.
To understand how you can help mitigate this risk, it is first important to understand how BGP prefix advertisements and BGP hijacking work.
How BGP advertises prefixes
BGP organizes the internet into ASes. Each AS is comprised of multiple routers, and contains within its borders specific prefixes, or routes, that it advertises to neighboring ASes. BGP routers propagate these prefixes throughout the internet and maintain a path to that destination through various ASes. Each AS is responsible for announcing to its neighbors the prefixes that it owns and contains within it.
The result is a BGP table maintained within each BGP router that contains the path of ASes that must be traversed to reach that particular prefix.
For example, consider the following diagram:s on your internet routing.
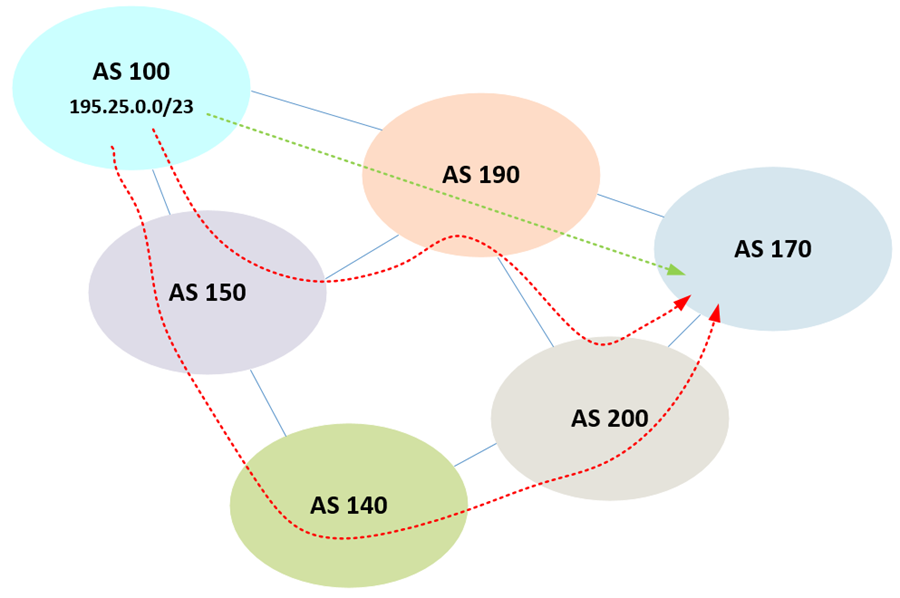
AS 100 is advertising its own prefix of 195.25.0.0/23 to neighboring ASes. When that information reaches AS 170, it will say:
- Prefix: 195.25.0.0/23
- AS_PATH: AS100 AS190
Now, AS 170 will have received this prefix from advertisements with different paths, as shown by the red dotted lines. However, assuming all previous BGP attributes remain the same, because those paths are longer, that is, they traverse a larger number of ASes, the green dotted line path wins out. We’ll see later on why this is important when it comes to hijacking.
Remember the ASes shown in the diagram are composed of many routers. Those on the edge of the AS that form peerings with BGP routers in other ASes are External BGP or eBGP routers. eBGP routers are responsible for announcing prefixes to other ASes.
What is a BGP route hijack?
A BGP route hijack occurs when a “hostile” AS decides to advertise a prefix that is not its own. For example, in the following diagram, AS 140 is illegitimately advertising the same prefix as AS 100:
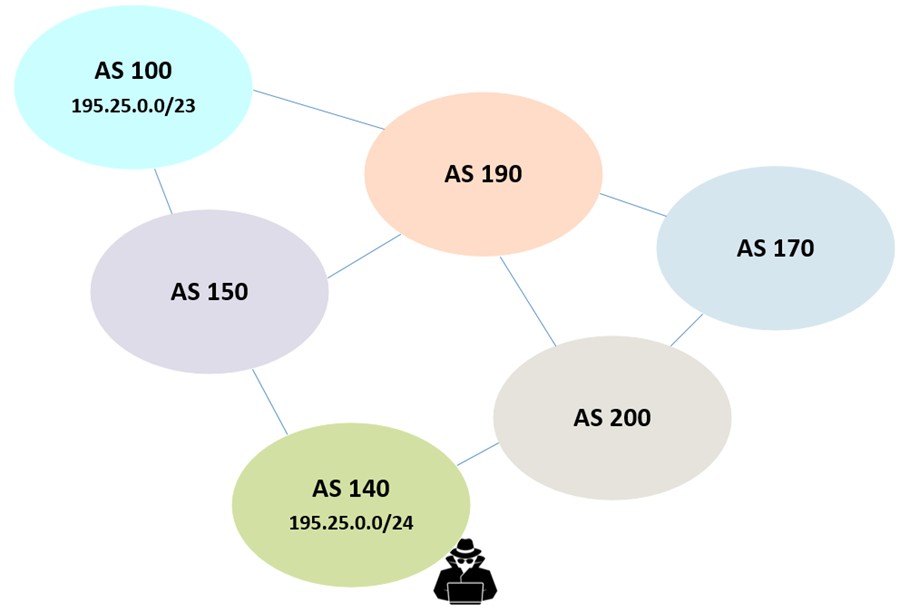
What will happen? All other ASes will receive two different advertisements of the same prefix. Which one they select to put in their BGP table depends on the BGP attributes.
The AS_PATH length attribute’s role in BGP hijacking
One of the attributes that will play a large part in this decision is the AS_PATH. Assuming all previous attributes remain the same, the route with the shortest AS_PATH will be installed. If the AS_PATH is equal, then other attributes act as tie-breakers, such as oldest path or router ID, which leads to unpredictable routing.
In the case of the above diagram, only AS 190 is assured of having correct routing to the 195.25.0.0/23 prefix. The others will either have AS 140 as the destination or will have unpredictable results due to AS_PATH tiebreakers.
In addition, hijackers can perform what is known as an AS_PATH forgery, where the advertised AS_PATH for the destination is modified so that traffic destined for the route in question will go through the local AS. In these cases, the legitimate AS is included in the AS_PATH to make it more difficult for such a hijack to be detected while traffic is steered towards the illegitimate AS.
Prefix mismatches and BGP hijacking
The term “prefix” in the context of BGP can be used in various ways, including referring to specific routes. Strictly speaking, the prefix is the subnet mask in “/” notation (a.k.a. CIDR notation) that specifies the actual size and range of IP addresses being advertised. BGP can advertise prefixes for sizes /8 to /24.
If an AS owns the 147.52.0.0/24 prefix, and it erroneously advertises it with an incorrect prefix of 147.52.0.0/23, it will begin advertising an address space that does not belong to it.
Similarly, if we look at our previous example of malicious BGP hijacking, if our hijacker decides to use a prefix of /24 as shown below, then he will be able to steer all traffic within the 195.25.0.0/24 network to itself.
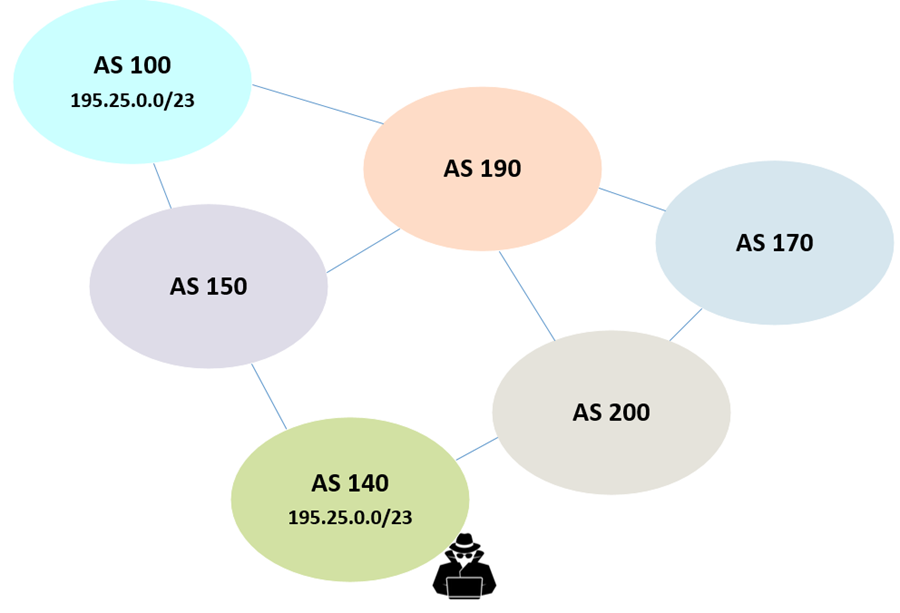
Remember that BGP will always prefer placing a more specific prefix into its routing table. The result is that all other ASes receiving these advertisements will see AS 140 as the owner of the 195.25.0.0/24 network and will route traffic accordingly.
Why do hijackers hijack?
There are multiple reasons an attacker may perform BGP route hijacking. The Amazon example at the beginning of this article is a textbook example of financial motivations. Other reasons an attacker may perform BGP route hijacking include:
- Denial of service to particular online services.
- Redirection of traffic to counterfeit web pages to achieve phishing of credentials, credit card numbers, and other confidential information.
- Redirection of traffic to overwhelm certain services.
- Disruption for disruption’s sake, some attackers carry out attacks simply because they can.
How to protect against BGP route hijacking
As you can see, hijacking is a very real, potential threat to the correct operation of routing on the internet. For this reason, it is important to employ the appropriate mechanisms and configurations to protect against these kinds of attacks and accidents.
How do you prevent BGP route hijacks?
The short answer is you can’t. There is no way to prevent someone from configuring a BGP router to hijack routes, either purposefully or accidentally. Techniques for dealing with hijacks have to do with detection, mitigation, and limitation of the propagation of incorrect routes. These techniques are described below.
Prefix filtering
ISPs should filter BGP advertisements and only allow those containing legitimate prefixes from being propagated further. IP advertisements should not be accepted as they come. Instead, they should go through a filtering process that uses algorithms to detect hijacks and validate legitimacy.
Similarly, in most cases, BGP routers should only announce their prefixes to select networks, not to the entire internet. Limiting announcements helps prevent hijacking that can result from misconfigurations and accidents.
While useful, prefix filtering alone is not enough. Administrators must always supplement it with additional measures.
BGP hijacking detection
Hijack detection can take several forms. Initially, changes in baseline performance, such as greater latency, misdirected traffic, or general degradation of performance are initial signs that may indicate some form of hijacking. Additionally, monitoring of advertisements, as well as recording the availability and downtime of routes are important aspects involved in discovering a hijack.
More sophisticated systems can also analyze the advertised ASes from neighbors to see if hijacked prefixes are included in the advertisements, can identify prefix mismatches, and use path analysis to ensure correct routing, all in near real-time.
Securing BGP
BGP was first developed in 1989. Since then, it has been developed and vastly improved. However, security has not been part of its improvements. Some attempts have been made to incorporate security with the introduction of BGPsec in 2017 but there has not been any substantial adoption. So, for now, this thirty-something protocol remains inherently vulnerable and requires somewhat elaborate monitoring mechanisms to keep it in check.
One aspect that has the potential to aid in the fight against BGP route hijacking is the use of a Route Origin Authorization (ROA). ROAs are cryptographically signed objects that can be used to validate if a particular prefix has been originated from a legitimate AS. ROAs are created by each AS owner in cooperation with the Regional internet Registry (RIR), which provides the RPKI infrastructure needed to generate them. More information about this can be found at the American Registry for internet Numbers (ARIN) website.
Conclusion
It is rare to find a vital technology such as BGP that is so vulnerable to the effects of malicious attacks or accidental misconfigurations. And yet, BGP, when paired up with the appropriate monitoring or observability solutions that reliably detect and mitigate against the effects of route hijacks, is more than sufficient to deliver the routing services that the internet needs.
CHAPTERS
NEWSLETTER
Subscribe to our newsletter
Get the latest blogs, whitepapers, eGuides, and more straight into your inbox.
SHARE
Detect BGP anomalies before attackers exploit them.
LogicMonitor’s network monitoring capabilities provide real-time visibility into routing changes and anomalies, helping your team detect unauthorized prefix announcements and act before traffic is redirecte
FAQs
What is BGP hijacking?
BGP hijacking (also called prefix hijacking or route hijacking) occurs when an autonomous system (AS) illegitimately announces IP prefixes that belong to another organization. Because BGP routers accept route announcements from peers without verifying ownership, other ASes propagate the fraudulent route globally. This can redirect internet traffic away from legitimate destinations, enabling eavesdropping, traffic interception, or service disruption.
What is the difference between BGP hijacking and a route leak?
Both involve incorrect route propagation, but for different reasons. A route leak is typically accidental, an AS propagates routes it received from one peer to another peer without intending to, violating routing policy. A BGP hijack is deliberate, with an AS fraudulently claiming to be the origin of prefixes it doesn’t own. Route leaks can also be exploited maliciously, but the distinction lies in intent and mechanism.
How does RPKI prevent BGP hijacking?
RPKI (Resource Public Key Infrastructure) allows IP address holders to cryptographically sign Route Origin Authorizations (ROAs) that specify which AS is authorized to announce a given prefix. BGP routers with RPKI validation enabled can check incoming route announcements against the ROA database and reject routes that fail validation (invalid origin AS or prefix length). RPKI doesn’t eliminate all hijacking scenarios but significantly raises the bar for fraudulent announcements.
How can I monitor for BGP hijacking of my own prefixes?
The most effective approach is to monitor your own prefixes from multiple external BGP vantage points, not just your own routers. Public data sources like RIPE NCC’s Routing Information Service (RIS) and RouteViews provide BGP data from hundreds of global peers. You should alert on any unexpected origin AS announcing your prefixes, unexpected AS_PATH changes, or more-specific (sub-prefix) announcements of your address space from ASes you don’t control.
© LogicMonitor 2026 | All rights reserved. | All trademarks, trade names, service marks, and logos referenced herein belong to their respective companies.

