DNS Tunneling
DNS tunneling encodes data in DNS queries to bypass security controls. Here is how attackers do it, and how to detect and stop it.
Denton Chikura

The quick download:
DNS tunneling exploits a protocol most firewalls leave open, making it a preferred channel for data exfiltration and command-and-control communication.
-
Attackers encode data inside DNS queries and responses, bypassing traditional network security controls.
-
Detection requires monitoring DNS query volume, payload size, entropy, and the frequency of requests to unusual domains.
-
Blocking DNS tunneling requires DNS inspection at the resolver level, not just firewall rules.
-
Configure DNS resolvers and monitoring tools to baseline normal query behavior, then alert on anomalies such as high-entropy subdomains, oversized payloads, and frequent lookups to newly observed or suspicious domains.
The Domain Name System (DNS) is one of the most important technologies used on the Internet and in networking in general. This is the system that translates IP addresses into human-friendly domain names, also called Uniform Resource Locators (URLs), so that people can access websites more easily. DNS is necessary because humans are much better at being able to remember something like logicmonitor.com than they are at memorizing an IP address—especially since IPv6 addresses are 128 bits long!
Because DNS has been an essential technology for years, it has also been looked at closely by hackers trying to find attack vulnerabilities. One of the most damaging types of DNS attack is known as DNS tunneling.
What Is DNS Tunneling?
DNS tunneling is a type of attack exploiting the Trojan horse concept where hackers embed malicious code or programs into a message that appears to be a DNS request. Since DNS is an essential component of most network and internet activity, this type of traffic is often able to pass through firewalls and other systems without much scrutiny.
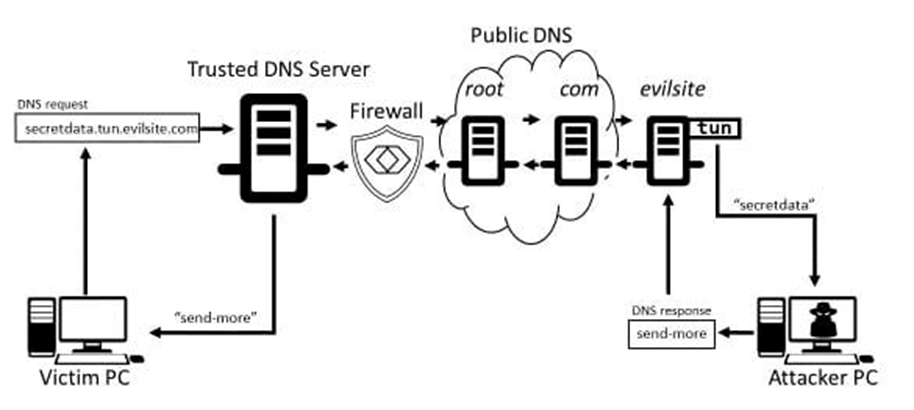
The following is a basic outline of how a DNS attack is conducted:
- Register a Host Domain: A hacker registers a domain and may even put up a legitimate-looking site. On this site, the hacker will also have DNS tunneling malware programs installed and ready to be distributed when accessed.
- Infect a Target Computer with Malware: The next step, which is often the most difficult, is to get a computer within the target network infected with malware. This can be done in many different ways, including using other infected websites, infected emails, or even compromised hardware brought into a company’s facility.
- Connect Infected Computer to the Hacker’s Website: When ready, the infected computer will attempt to connect to the hacker’s website. Part of this connection is sending a DNS request to locate that website. DNS requests are always allowed to go through firewalls, giving the hacker a basic connection into the otherwise protected systems.
- Pass Malicious Code Through DNS Resolver: Once a connection is established and approved, the hacker’s host server can pass additional code or programs into the target network. This code can be used to collect data, place programs onto systems, or do any number of other things that can allow the long-term exploitation of the compromised systems.
Here is a basic diagram of how this process works:
Attacks Related to DNS Tunneling
One of the most important things to note about DNS tunneling attacks is that the hackers don’t generally perform this type of attack as an end goal. Instead, they use a successful DNS tunneling attack as a way to complete other malicious acts. In addition, unlike some other types of hacking, the actual DNS tunneling action is not the first step in the attack.
DNS tunneling should be seen more as a hacking tool or strategy that is used as a part of other malicious activities. The following are some types of attacks that are often associated with DNS tunneling.
| Attack Type | Brief Description | Relation to DNS Tunneling |
|---|---|---|
| Malware Installation | Installing a virus or malware program on a computer within a network. This can be done in many ways, ranging from sending infected emails to getting a user to insert a compromised USB drive. that will install the malware on a system. | This is normally the first step in a DNS tunneling attack. Proper virus and malware monitoring and removal is essential for avoiding DNS tunneling attacks. |
| User Credential Collection | The virus or malware can use keyloggers and other strategies to collect user IDs and passwords, which can be sent to the attacker. That information can be used either directly by the attacker to perform other actions or sold on the dark web for profit. | The user credentials can be collected through the compromised computer and then sent back to the attacker via the DNS tunnel that they have control of. |
| Network Footprinting | DNS queries can be used from within the infected network to build a system map. This map will identify what systems are being used and can potentially help create future vulnerabilities. This is important to hackers since they need this type of network map to plan additional activities. | Data from network footprinting is often fed to the hacker using the connections established with DNS tunneling. It can also be used by additional malware that is installed through the DNS tunneling attack to allow the harmful software to become more effective. |
| Data Theft | An unauthorized connection into the network can be used to begin transmitting even large amounts of data, including sensitive user data. This can be done using DNS tunneling, but more likely will be used with protocols such as SSH and FTP and triggered or controlled through the DNS tunnel. | Hackers use a variety of techniques to collect and distribute sensitive data. These techniques are often controlled through the compromised DNS tunnel. |
| Communication Control | Being able to communicate with and control the malware or other infected systems is an essential part of many types of attacks. | Advanced DNS tunneling toolkits will perform regular “check-ins” with the hacker’s host server to maintain communication and receive additional commands.The continuous checking in with the host server allows the hacker to perform actions long into the future. This means that a DNS tunneling attack is not just a single event but a long-term threat that could have impacts lasting for years. |
While these are some of the most common types of attacks that are related to DNS tunneling, they are far from the only ones. Almost every type of hacking attempt can benefit from either putting malware in place or being able to exploit a connection. This is why DNS tunneling toolkits are among the most commonly used resources for advanced hackers.
How to Detect a DNS Tunneling Attack
Detecting a DNS tunneling attack can be difficult. Fortunately, there are ways to identify when this type of attack is happening so that you can take action to stop it.
The first step in detecting a DNS tunneling attack is making sure that you are using an advanced antivirus/antimalware program, which is essential for avoiding most types of security threats. Beyond that, you need to make sure that you have systems in place that will perform deep scans of all traffic, including DNS requests.
These tools need to look at all types of traffic coming in and out of the network These tools should look for behavior like unusual destinations for traffic as well as spikes in traffic, and they should examine what is being transmitted to see if anything is out of the ordinary.
The size of the request and response can help reveal a suspicious DNS tunneling attempt. Since extra bytes are inserted in the packet header as part of DNS tunneling, monitoring the ratio of the bytes used in the source field to the bytes used in the destination field can help detect a suspicious activity. Detection tools capture the packets, store the byte counts, and measure the ratio looking for an usual change.
Another technique used for detecting suspicious DNS tunneling activity is to count the number of characters used in the label field (up to 63 characters) or the name field (up to 255 characters) of the DNS requests. DNS tunneling uses the label and name fields to transfer data back and forth as part of the DNS requests and responses.
Another option to consider is setting up and managing your own private DNS servers. Most internet connections rely on public DNS servers, which generally work well, but are outside your control. When you run your own DNS servers, you can have access to much more information related to sites that are accessed, redirected traffic, suspicious patterns, and much more.
DNS Monitoring Tools
As you might expect, DNS monitoring tools are critical for trying to detect DNS tunneling attacks. DNS traffic is unique in that while it is generally very small in size, it is also extremely important. In addition, virtually every connection to the Internet involves some type of DNS traffic at some point. This means that the DNS traffic is routed and secured differently than other types of network traffic, which makes it vulnerable to attack.
How to Protect Your Network Against DNS Tunneling
The best thing that you can do to protect your network against DNS tunneling is to make sure you have a comprehensive security plan in place. Since this type of attack not only requires the external attacker to have the right tools but also an infected device inside the network, protection will require a number of different steps. Some key mechanisms that you should have in place to minimize your risk of a DNS tunneling attack include the following:
- Updated Virus and Malware Protection: A good antivirus and antimalware strategy is absolutely essential for any corporate network. Using a proven system, and keeping it updated, will help to stop DNS tunneling attacks before they begin by preventing systems from being infected.
- Advanced Network Traffic Monitoring: Advanced network traffic monitoring tools look for all types of potentially malicious traffic, including DNS packets. This will help to identify this type of attack very early on so that it can be stopped.
- Network Insight Tools: Use these tools to look not just for what type of traffic is going through your network but also how much of it is important. Long-term monitoring of all types of network traffic will help your tools to be able to better identify changes and take actions to stop any unauthorized activity.
- Employee Training: The weakest point in any computer system is the set of behaviors of humans accessing the network. Keep your systems safe from DNS tunneling attacks by training your employees to avoid clicking on unapproved links, opening suspicious email, and taking other actions that could invite malware.
Take Steps to Prevent a DNS Tunneling Attack
DNS tunneling attacks have been around for a long time, and they will continue to be a serious threat long into the future. If you are responsible for any type of corporate network or system with any valuable information, taking steps to prevent this type of attack is much easier than trying to stop an attack in progress. Take the time today to understand how DNS tunneling attacks work and how they can be stopped.
CHAPTERS
- Network admin’s guide to synthetic monitoring
- Internet Exchange Point
- IT Transit
- The Benefits and Challenges of SD-WAN Architecture
- Free Online Network Tools Every Engineer Should Bookmark
- SD-WAN vs MPLS
- MQTT Broker
- Inter-VLAN Routing
- DNS Sinkhole
- How to Read a Traceroute
- Switching Loops
- SD-WAN Security
- IP Multicast
- DNS Tunneling
NEWSLETTER
Subscribe to our newsletter
Get the latest blogs, whitepapers, eGuides, and more straight into your inbox.
SHARE
Get visibility into what your DNS traffic is really doing.
LogicMonitor monitors DNS infrastructure health and query patterns to help security and network teams detect anomalies that signal tunneling, exfiltration, or misuse.
FAQs
What is DNS tunneling?
DNS tunneling is a technique that encodes non-DNS data inside DNS query and response packets. Because most networks allow DNS traffic outbound, attackers use tunneling to establish covert channels that bypass firewalls and data loss prevention tools.
How do attackers use DNS tunneling?
An attacker establishes a malicious DNS server and registers a domain pointing to it. Malware on a compromised machine encodes data in DNS queries, embedding it in long subdomain strings. The attacker’s DNS server receives these queries, decodes the payload, and can respond with commands.
How do you detect DNS tunneling?
Detection relies on behavioral analysis. Key indicators include unusually long subdomain strings (often 100+ characters), high query volumes to a single domain, frequent use of uncommon record types like TXT or NULL, and large response payloads.
How do you prevent DNS tunneling?
Prevention involves: restricting DNS resolution to authorized internal resolvers, deploying DNS monitoring tools that detect behavioral anomalies, using DNS firewall solutions that identify known tunneling tools, and implementing network segmentation to limit outbound DNS requests.
© LogicMonitor 2026 | All rights reserved. | All trademarks, trade names, service marks, and logos referenced herein belong to their respective companies.

