Disclaimer: This content applies to the legacy UI and is no longer maintained. It will be removed at a future time. For up-to-date content, see Delinea Vault Integration. At the time of removal, you will automatically be redirected to the up-to-date content.
Integrating with Delinea Vault
Last updated - 25 July, 2025
Note: Thycotic has now been rebranded as ‘Delinea’. Although we have replaced Thycotic with Delinea in Support documentation, you will still find ‘Thycotic’ in some configuration properties.
LogicMonitor stores sensitive information including credentials, secrets, etc., for hosts, devices, services. LogicMonitor also offers integration with Credential Vault and provides better control over credentials management to users using their own Credential Vault. The LogicMonitor Collector provides the integration with Delinea as a Credential Vault solution. For more information, see Delinea Secret Server documentation.
Prerequisites
- The Delinea Vault Integration requires EA Collector versions 30.102 or higher. For more information on integrating the Delinea Vault with LogicMonitor Collector, see Integrating Credential Vault Properties.
- Verify access of Delinea Secret Server API using Postman client. For more information, see Delinea Secret Server REST API.
Delinea Secret Server REST API:
The Delinea Secret Server publishes REST API to manage various entities. For more information, see https://docs.delinea.com/secrets/current/api-scripting/rest-api-reference-download/index.md.
The Secret Server (SS) REST API guides are version-specific. Please ensure you refer to the correct version Secret Server guide.
The LM Delinea Secret Server integration uses the OAuth2 token-based REST API of the Delinea Secret Server. In this approach, you receive the OAuth2 token for authentication, which is used to perform the various entity operations of the Delinea Secret Server.
Configuring Delinea Vault
To configure the Delinea vault, complete the following steps:
1. Configure the vault properties on the devices. The properties consist of the vault metadata and vault keys. For more information, see the Delinea Vault properties section.
2. Once the vault properties are configured, set the vault.bypass agent configuration as false.
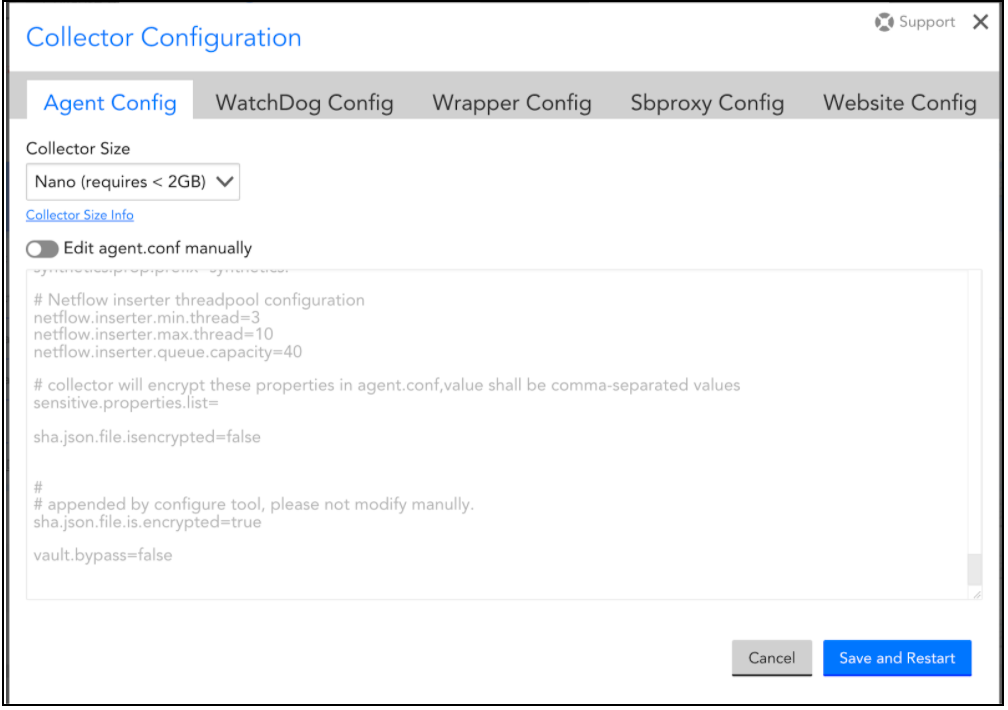
Note: You can change the default agent configuration settings as required. For more information, see Delinea Collector Agent Configuration Settings
Delinea Collector Agent Configuration Settings:
The below table contains the collector agent configuration related to the vault.
| Agent Configuration Property/Type | Type | Default Values | Description |
| vault.bypass | Boolean | True | If the value is set as true, the vault API will not be called. If the value is set as false, the vault API would be called. |
| vault.thycotic.session.timeout | Integer | 20 minutes | The property specifies the interval in the minutes, for which the OAuth2 access token is valid. Once this duration has elapsed, the token becomes invalid. |
| vault.thycotic.max.tokenrefresh.allowed | Integer | 3 | The property specifies the maximum number of token refreshes allowed. The token refresh can be done to get the access token for the user using the refresh_token information(without using the user credentials). |
| vault.thyotic.secret.path.name.id.cache.expiration | Integer | 20 minutes | The property specifies the expiration duration for the cache that maintains the Secret Path (FolderName, SecretName) → Secret Id mapping. The Secret Path mapping approach of the lmvault keys uses this cache internally to retrieve the secret id based on the secret path. |
You can view the agent configuration properties by navigating to Settings > Collector > click the gear next to the required collector name > Support > Collector Configuration.
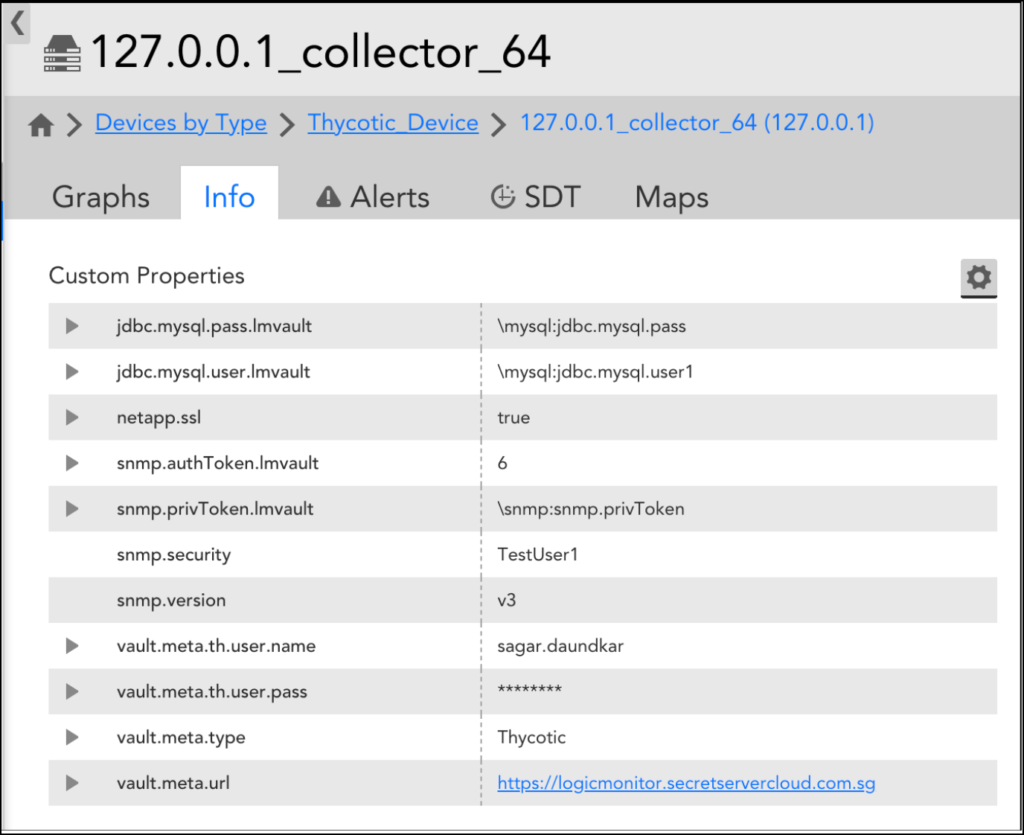
Delinea Vault properties
Vault properties, such as Vault Metadata and Vault Keys for the Collector, can be configured at the device or device group level.
Vault Metadata
The following table lists the Vault Metadata properties.
| Vault Metadata | Description |
| vault.meta.url | The URL of the vault. This URL should contain the folder and application ID only. |
| vault.meta.type | The type of the vault. Use the value as Thycotic to connect to the Delinea Secret Server. |
| vault.meta.th.user.pass | The password for the Delinea Secret Server account. This password would be used to get the bearer authentication token using Secret Server OAuth2 API. |
| vault.meta.th.user.name | The username for the Delinea Secret Server account. This username would be used to get the bearer authentication token using Secret Server OAuth2 API. |
| vault.meta.header | The headers required for HTTP Get Request. The value for this custom property would be the header separated with “&“ the header key value would be separated with “=” as shown in the below example:vault.meta.header – Content-Type=application/json&Accept-Encoding=gzip, deflate, br |
Configuring Delinea lmvault.keys
You can configure lmvault.keys in the following three ways: secret id, secret path, and a combination of secret id and secret path.
- Secret id—lmvault key value can be configured with the secret id. This is the most efficient method and is recommended by Delinea.
- Secret path—LogicMonitor provides another out-of-the-box approach for configuring the lmvault.key value. lmvault value consists of the secret path and secret name.
LogicMonitor calls the Delinea API to get the secret id for these secret paths, and these secret ids are further used for the credentials retrieval.
Note: As this approach requires additional API calls, you must use this approach only when required.
Example:
LogicMonitor provides the two approaches for the secret id retrieval using the secret path:
- Default Approach—LogicMonitor searches for the folder and Secrets. In this approach, the folders and the secrets are searched to form the secret_path_name relation with secret id.
- Delinea Reporting—LogicMonitor uses Delinea reporting to retrieve the secret id using a secret path. This is an efficient approach for the secret path as compared to the Default Approach.
Note: Ensure that you can access the Delinea Report “What secrets a user can see” in the Delinea Secret Server portal. For more information on configuring the Delinea reports, see Configuring Delinea Report Properties.
- A combination of secret ID or secret path along with a Delinea field—You can configure devices to pull the secret values for a property from the secret ID or secret path. The field name is attached to the property to fetch the secret value from the Delinea field. The
.lmvaultproperty is configured to have the information of the Delinea field appended within the enclosed symbol “<>” at the end. You can use the templateRecordID<FieldName>/RecordPath:Name<FieldName>. For example,
| Vault Property | Customised Field |
ssh.user.lmvault | 9<username> |
ssh.pass.lmvault | 9<password> |
snmp.security.lmvault | 15<snmpsecurity> |
snmp.privToken.lmvault | 15<privtoken> |
ssh.pass.lmvault | \allsecrets\ssh:ssh.pass<password> |
Configuring Delinea Report Properties
To configure Delinea report properties, complete the following steps:
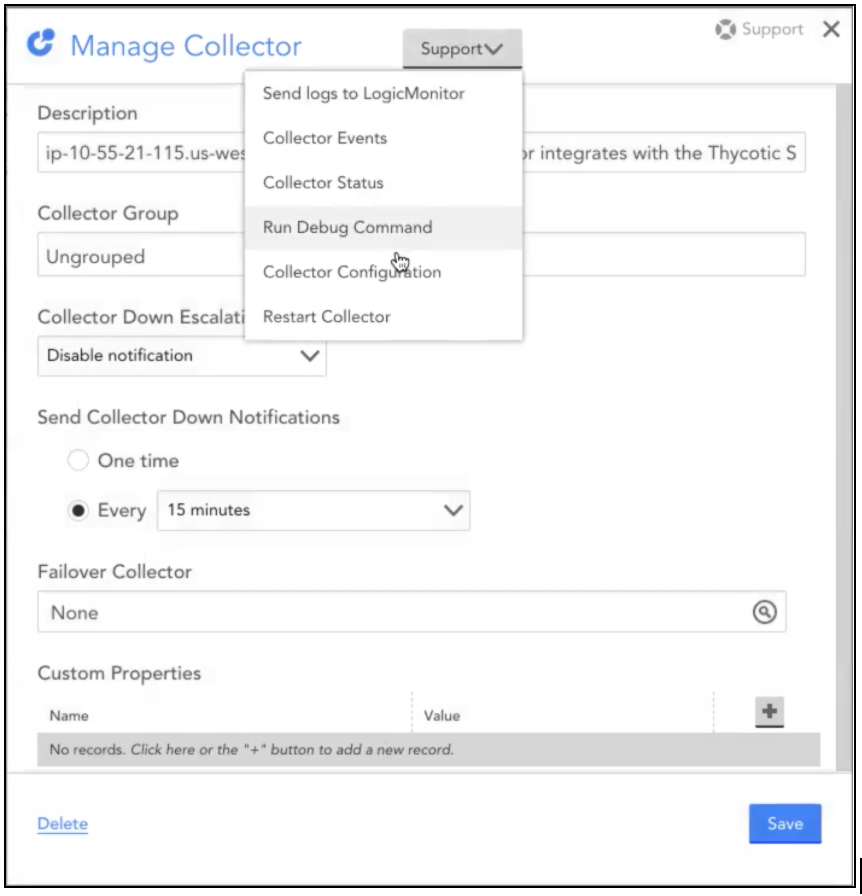
1. Navigate to Settings > Collector > select the required collector and click the Gear icon.
2. On the Manage Collector dialog box, select Collector Configuration from the Support drop-down list.
3. Click the Agent Configurations tab and enter the following Delinea report properties :
| Name | Type | Default | Details |
| vault.thycotic.secret.report.access.enabled | Boolean | false | The property specifies whether Delinea secret server report access is enabled or not. Ensure that all the access for the reporting is granted before enabling this boolean property, Otherwise, it may result in an API Access Denied issue. This access consists of access to users, reports, etc. |
| vault.thycotic.secret.report.id | Integer | Note: You must provide the correct report id value. | The property specifies the value of the report id of the report “What Secrets a User can see”, which is a system report for secrets. |
Troubleshooting
1. How to confirm API using postman?
Ans: The LogicMonitor Delinea Secret Server integration uses the OAuth2 token-based REST API of the Delinea Secret Server. You will receive the OAuth2 token for authentication, which is used to perform the various entity operations of the Delinea Secret Server. The APIs can be confirmed using the postman. To confirm APIs using Postman, refer to the following images:
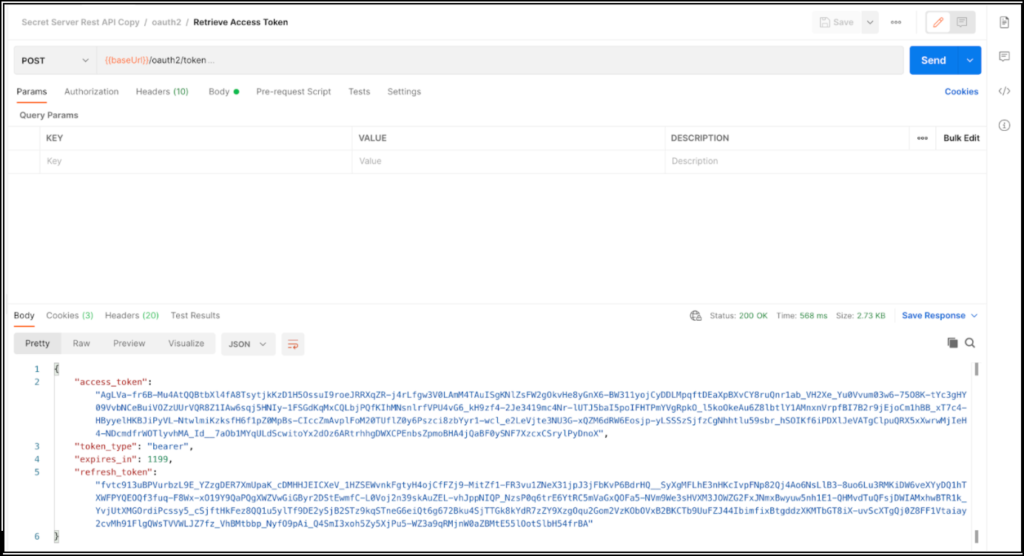
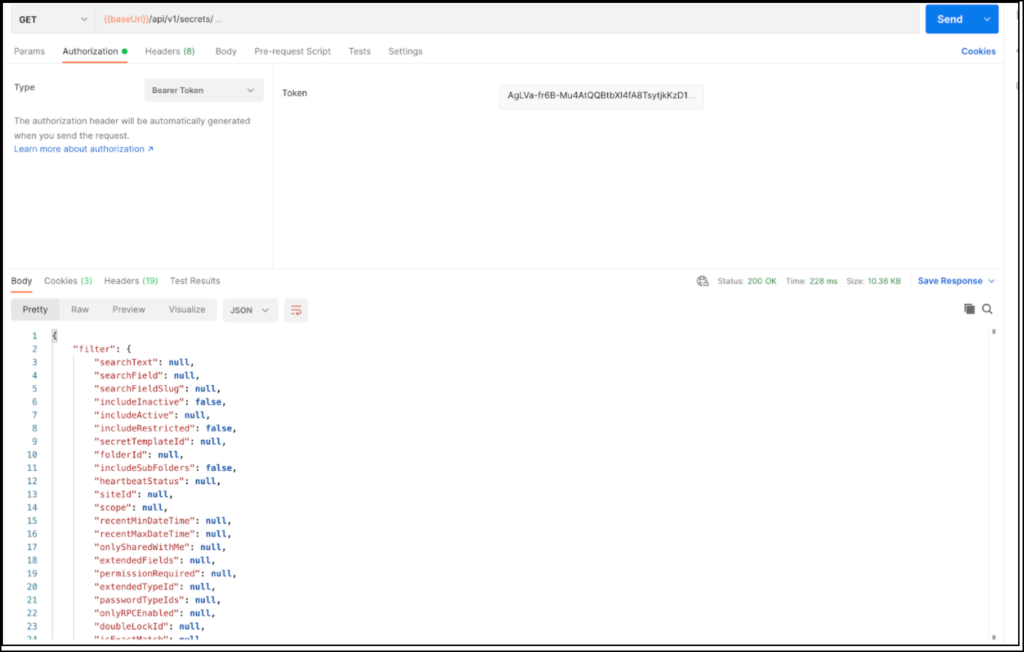
Note: For more information on REST APIs, see Delinea Secret Server REST API.
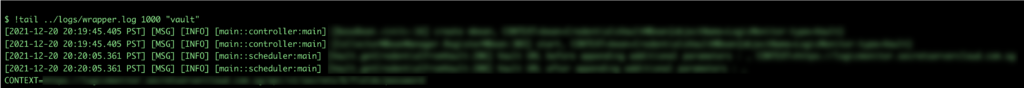
2. How to get collector vault logs?
Ans: To get the collector vault logs, use the !tail debug command. The vault logs are a part of the wrapper.log file, which you can directly access. For more details, refer to the following screenshot:
3. How to enable the debug logs for the vault to get more data?
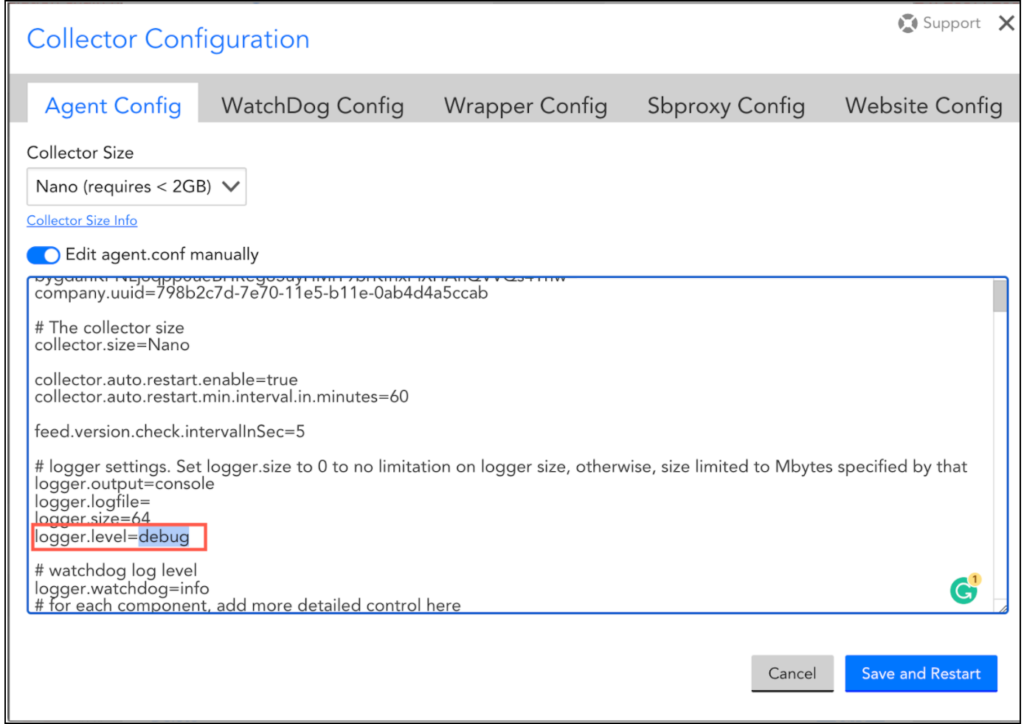
Ans: To enable the debug logs for the vault, complete the following steps:
1. Navigate to Settings > Collectors > select the required collector.
2. On the Manage Collector, select Collector Configuration from the Support drop-down list.
3. Click the Agent Config tab and set the logger.level value as debug.
4. Once you have added the configuration details, click on Save and Restart.
Refer to the following image: