Configuring Collector to Communicate with HTTP Proxies
Last updated - 15 October, 2025
If your environment does not allow Collector to directly connect with LogicMonitor data centers, you can configure the Collector to communicate through an HTTP proxy.
Updating SSL and Proxy Settings
By default, Collectors are not configured to use proxies. To communicate with HTTP proxies, you must make updates to several proxy settings located in the agent.conf settings. For more information, see Editing the Collector Config Files.

Once updated, the new settings look similar to the following:
# Proxy settings
ssl.enable=true
proxy.enable=true
proxy.host=10.0.0.54
proxy.port=8080
proxy.user=domain\username
proxy.pass=password
proxy.exclude=
proxy.global=falseThe new settings designate the following:
ssl.enable=trueindicates that the Collector makes outbound connection using SSL.proxy.enable=trueindicates that the Collector uses the proxy settings.proxy.host=indicates the IP address of the proxy server.proxy.port=indicates the port the proxy server uses.proxy.user=indicates the username the Collector uses when connecting to the proxy.proxy.pass=indicates the password the Collector uses when connecting to the proxy.
Note: The specified settings reflect a Windows-based proxy requiring authentication. Windows Collectors support NTLM and other native Windows authentication methods. Linux Collectors support only basic authentication.
Changing Proxy Password
If a proxy server has password-based authentication, its credentials are stored in the proxy.user and proxy.pass fields. The proxy password is encrypted.
- In LogicMonitor, navigate to Settings > Collectors.
- In the Collectors tab, select a Collector to configure.
- Select
 More and then select Collector Configuration.
More and then select Collector Configuration.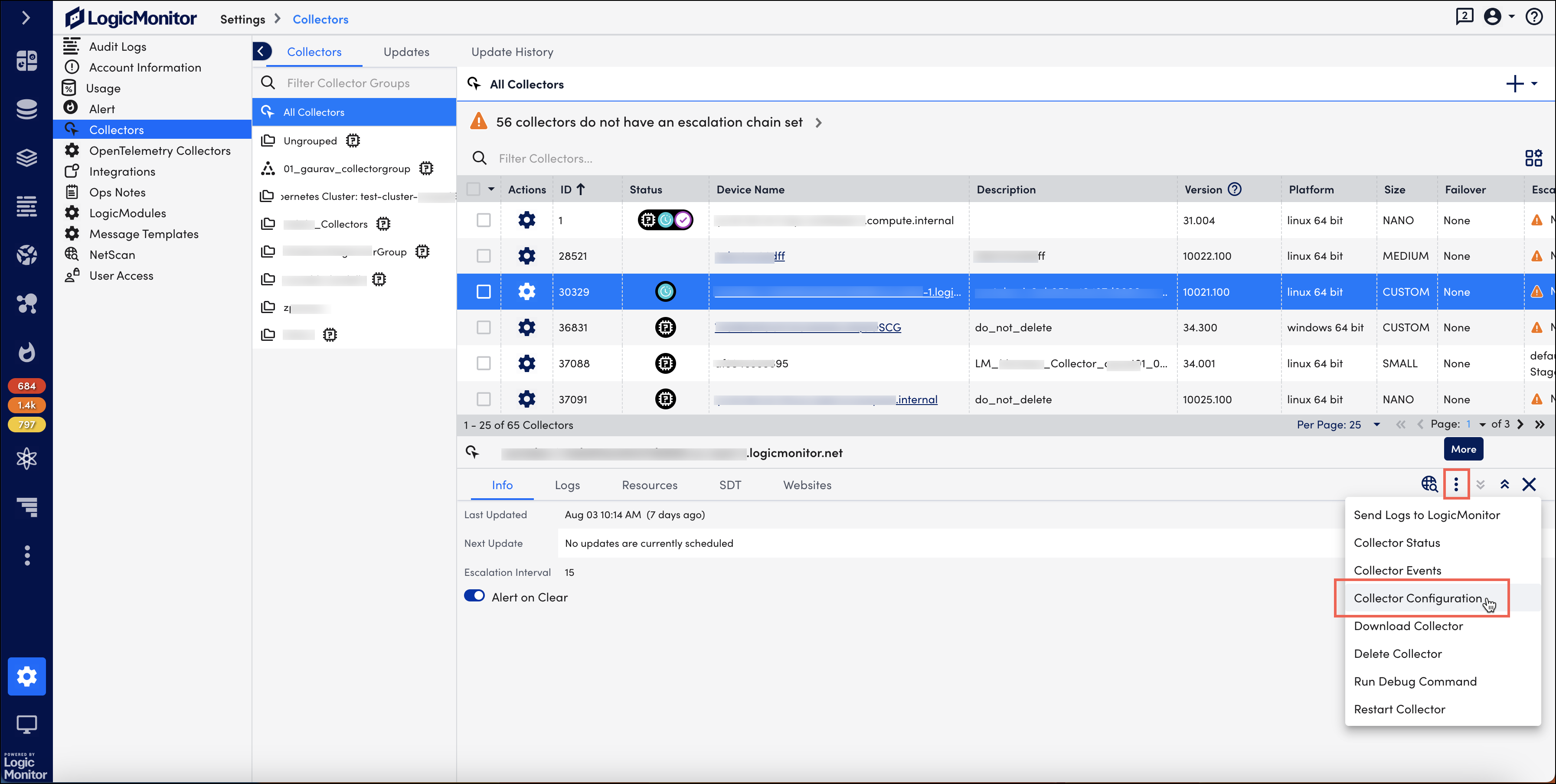
On the Collector Configuration page, the agent.config settings are displayed. - Scroll to locate the proxy settings.
- Enter a new password in plain text in the
proxy.passfield.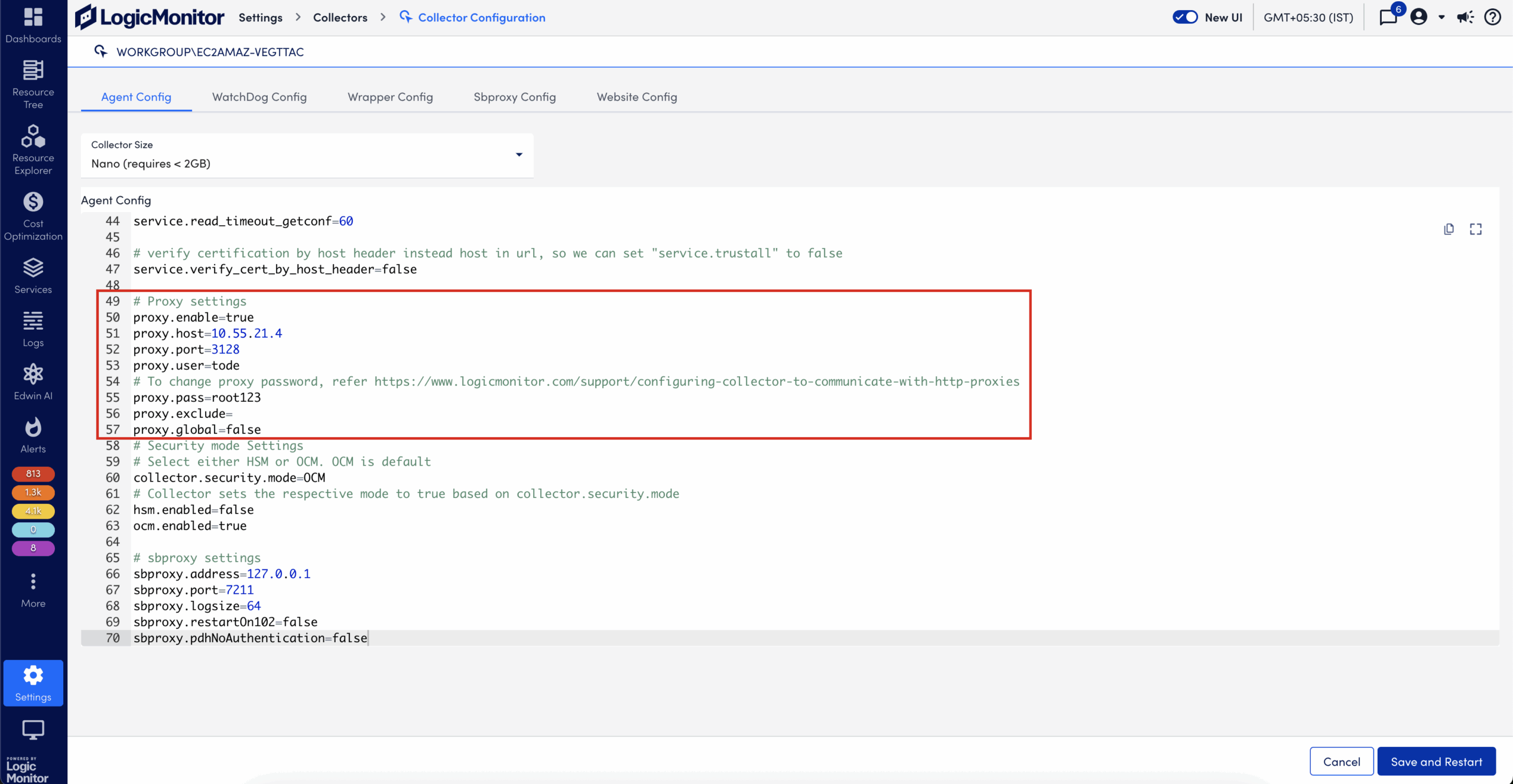
- Select Save and Restart.
Troubleshooting Collector Proxy Configuration
We have highlighted some common issues experienced (and how to resolve them) when configuring Collectors to be used with HTTP proxies.
Proxy Authentication Required Issue
When Collector is configured to use proxy that requires basic authentication, the Collector may throw the following exception:
[MSG] [WARN] [main::controller:main] [Controller2._initConfiguration:461] Unexpected status encountered from server. Will retry., CONTEXT=retry=30s, statusCode= 500, errMsg=Unable to tunnel through proxy. Proxy returns "HTTP/1.1 407 Proxy Authentication Required"In this case, add the following configuration to the wrapper.conf setting:
wrapper.java.additional.16=-Djdk.http.auth.tunneling.disabledSchemes=Invalid SSL Certificate Issue
If a Collector does not get a valid SSL certificate issued directly from LogicMonitor, it fails to start properly. For example, all SSL certificates in the client environment are intercepted and reissued using security software such as Blue Coat Proxy.
[03-26 15:53:03.222 EDT] [MSG] [INFO] [statusmonitor:::] [StatusListener$1.run:106] Receive peer request, CONTEXT=command=keepalive, charset=windows-1252, peer=/***.***.***.***:******
[03-26 15:53:03.268 EDT] [MSG] [WARN] [statusmonitor::scheduler:] [PropertyFilePersistentHandler._load:94] task file not found, CONTEXT=filename=C:\Program Files (x86)\LogicMonitor\Agent\conf\persistent_task.conf, EXCEPTION=C:\Program Files (x86)\LogicMonitor\Agent\conf\persistent_task.conf (The system cannot find the file specified)
java.io.FileNotFoundException: C:\Program Files (x86)\LogicMonitor\Agent\conf\persistent_task.conf (The system cannot find the file specified)
at java.io.FileInputStream.open0(Native Method)
at java.io.FileInputStream.open(FileInputStream.java:195)
at java.io.FileInputStream.<init>(FileInputStream.java:138)
at java.io.FileInputStream.<init>(FileInputStream.java:93)
at com.santaba.common.util.scheduler.impl.PropertyFilePersistentHandler._load(PropertyFilePersistentHandler.java:88)
at com.santaba.common.util.scheduler.impl.PropertyFilePersistentHandler.<init>(PropertyFilePersistentHandler.java:30)
at com.santaba.common.util.scheduler.Schedulers.newPersistentScheduler(Schedulers.java:17)
at com.santaba.agent.collector3.CollectorDb._newScheduler(CollectorDb.java:172)
at com.santaba.agent.collector3.CollectorDb.<init>(CollectorDb.java:68)
at com.santaba.agent.collector3.CollectorDb.<clinit>(CollectorDb.java:65)
at com.santaba.agent.agentmonitor.StatusListener._getAgentStatusResponse(StatusListener.java:279)
at com.santaba.agent.agentmonitor.StatusListener$1.run(StatusListener.java:117) /
[03-26 15:53:03.947 EDT] [INFO] [1] [default] [controller] [Controller2._initHttpService:469] Agent starting with ID - 00baae57-3971-4239-9610-b512aae9c21csbagent
[03-26 15:53:04.232 EDT] [MSG] [INFO] [main::controller:main] [SSLUtilities.checkCertificates:160] Invalid or wrong SSL Certificates found, CONTEXT=info=Found total 2 certificates:
Subject: CN=*.logicmonitor.com, OU=Domain Control Validated
Issuer: CN=SSLInterception87
Type: X.509
SHA1: 9a:a6:ff:33:85:cc:13:4c:3a:13:11:77:5c:ef:5e:a7:74:65:6b:de
MD5: 61:35:08:b5:ec:71:a2:ae:05:c4:7f:54:f1:aa:6f:ad
Valid from: 2017-04-19 10:02:01 -0400
Valid to: 2020-06-18 17:33:09 -0400Subject: CN=SSLInterception3
Issuer: CN=BillyBob's-CA, DC=slhn, DC=org
Type: X.509
SHA1: 6b:a8:1f:61:7b:5d:f0:e4:ee:7e:6a:1b:bb:18:de:67:be:5c:44:1d
MD5: d0:fc:64:da:6f:9b:1f:8d:1a:52:64:dc:41:da:e7:1c
Valid from: 2017-08-09 15:08:18 -0400
Valid to: 2021-10-03 08:53:12 -0400 */
[03-26 15:53:04.232 EDT] [MSG] [WARN] [main::controller:main] [Controller2._initConfiguration:322] SANTABA SERVER ceriticates not trusted, CONTEXT=Host=generic-customer.logicmonitor.com, port=443Solution A (Preferred)
The local administrator can add the SSL certificate to your allow list so that it comes into the network unmodified by a proxy or firewall. This ensures security.
Solution B
Change the Collector configuration setting from:
EnforceLogicMonitorSSL=trueto
EnforceLogicMonitorSSL=falseWarning: Removing SSL enforcement lowers the security of the connection between your Collector and LogicMonitor and must be carefully considered before implementing.


