NetApp Cluster Mode Monitoring
We are happy to announce the arrival of NetApp cluster-mode monitoring. To enable cluster-mode monitoring in your account, you need to import the datasources and OID from the LogicMonitor core repository.
To import datasources:
- Navigate to Settings, and then click Datasources, eventsources, batchjobs, and netscans in the left pane.
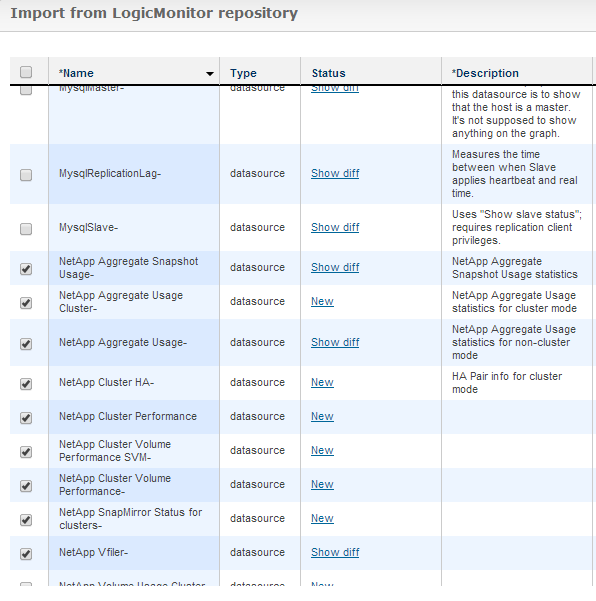
- Click Import > From LogicMonitor Repository.
- Click Submit on the Import from LogicMonitor repository credentials dialog.
- On the Import from LogicMonitor repository window, select all NetApp datasources. You need to import both the new Cluster mode datasources and your existing NetApp datasources. Updating your existing datasources prevents them from applying to cluster-mode devices.
Note: For most accounts, importing all Netapp datasources should not result in data loss. The only recent change in non-cluster datasources prevents them from applying to cluster-mode NetApps. If you have been a LogicMonitor customer for several years and have not updated your datasources, there is a risk that data points have been renamed or types changed from counter to derive. In this case, you can check the difference between the current datasources and your datasources. If there are datapoints that have been renamed, you may edit your datasources first, to make the names accord with the versions in the LogicMonitor Repository. Alternatively, you may just wish to modify the AppliesTo of your existing datasources manually, rather than importing the updated datasources.
Complete the following tasks to ensure appropriate monitoring of your NetApp cluster-mode devices:
- Import the NetApp cluster OID (.1.3.6.1.4.1.789.2.5)
- Set up your NetApps to ensure there is SNMP and API access. For more information, see “NetApp.”
- If you will be adding storage virtual machines (SVMs) to LogicMonitor as separate monitored devices (which is recommended), see “Enabling SNMP, API access on NetApp cluster mode SVMs.”
- We recommend adding each cluster node and each SVM to your LogicMonitor account. While cluster performance can be retrieved and monitored from any node, hardware and health information (such as spare and failed drives) requires each node to be added.
- Ensure you set the requisite authentication properties on your NetApp nodes as you add them to LogicMonitor.
- netapp.user
- netapp.pass for the API credentials
- SNMP.community
For Those Customers that Were Early Testers of the NetApp Cluster Monitoring
You should safely update your datasources to the current versions in the LogicMonitor repository. The new datasources provide some changes that improve presentation from early versions.
Additional User Interface Beta Features
We continue to work on the new user interface, stabilizing and enhancing the look and feel of the new LogicMonitor. Thank you to everyone actively using the new pages and submitting feedback. Keep the feedback coming, please.
Enforcing CUP-Based Authentication on Writable API Calls
With this release, LogicMonitor enforces the use of CUP-based authentication for API calls that can change data or configuration. This enforcement is to protect against cross-site request forgery (CSRF) attacks. Session-based authentication remains valid for read-based commands. Ensure any scripts which add hosts, delete hosts, modify accounts, or otherwise use the API to make changes to your LogicMonitor implementation are updated to use CUP-base authentication.
Issues
- Corrects a limit on custom alert text, expanding it beyond the 1024 limit to less than 65535.
- Fixes a regression in which Search Anything on the Alerts page searched columns but did not search the alert message.
- Resolves an issue where a java null pointer exception occurred when replying through email when no SMS recipients were defined.
- Corrects an issue occurring when granting a user role permission to remote session on a subgroup only. The Users section of the Account Management page no longer shows the remote session permission for that role as None.